The Blue Screen of Death. It scared everyone who saw it. Let’s just say CrowdStrike’s update to customers’ Microsoft systems did not go according to plan.
CrowdStrike later explained the error was attributed to a logic flaw in its Falcon sensor configuration update. Put differently, CrowdStrike claims it was a failure in its development process that caused the global problem and not a data breach at the hands of a third-party. However, the risks that came with the security vulnerabilities from this outage are not the only concerns that companies and CrowdStrike face in retrospect.
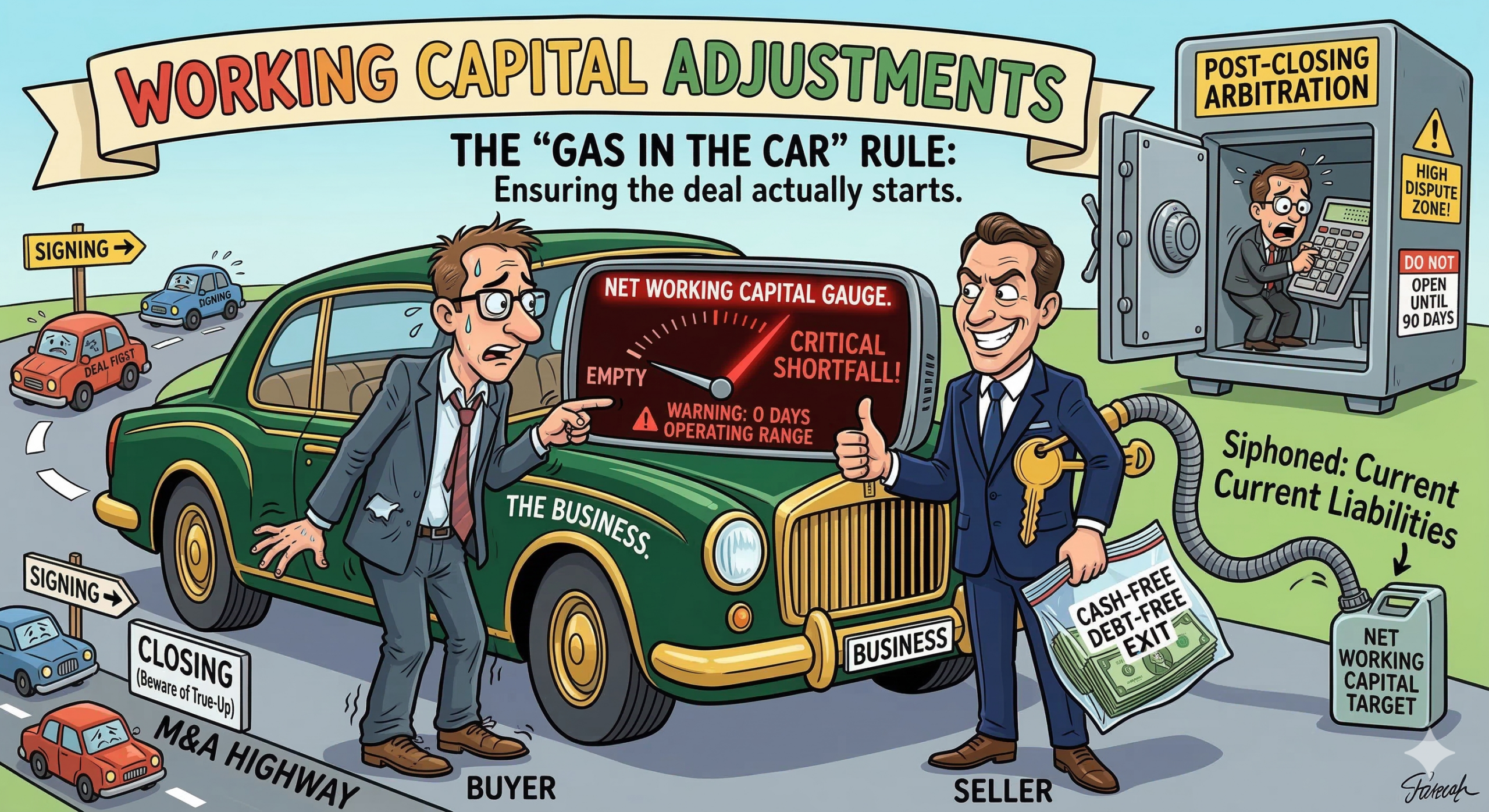
The CrowdStrike lawsuits reinforce the importance of contract negotiations in cybersecurity vendor engagements. Limitations of liability and choice of law provisions are two examples of important considerations in the negotiation process. Both companies and vendors need to think broadly when assigning liability to account for not only cyber-attacks but for technical and human errors as well. Therefore, the facts that trigger revisiting the terms of the agreement are no longer limited to data breaches including risks that both parties cannot control.
We previously addressed the key terms in SaaS contracts in a three part series: SaaS Agreements – Part 1 – Seidman Law; SaaS Agreements Part 2 – Seidman Law; and SaaS Agreements – Part 3 – Seidman Law. These articles are far more interesting to read after this clusterf**k of a situation. So are your existing SaaS and other contracts.
The Delta v. Crowdstrike legal theories add up to a classic law school exam question with too many issues to address within three hours. Here is an oversimplified version of the situation that highlights legal issues that are relevant to most SaaS customers.
Delta Airlines filed its lawsuit in Georgia state court against CrowdStrike. Delta’s claims include gross negligence, breach of contract, intentional misrepresentation or fraud by omission, and computer trespass. Of note, Delta claims it did not enable automatic updates yet CrowdStrike imposed the faulty update to Delta’s system without its consent. Delta further alleges gross negligence where CrowdStrike deployed the update without testing and staged deployments.
CrowdStrike struck back immediately in federal court in Georgia. Crowdstrike relied on the services agreement’s limitation of liability clause including a bar on “indirect, incidental, punitive, or consequential damages.” CrowdStrike further petitioned the court to declare CrowdStrike neither grossly negligent nor having committed willful misconduct to limit the amount of damages that can be recovered. Although the Georgia state court is the venue agreed upon by the parties, CrowdStrike argues that the venue in Georgia federal court is proper because federal laws are implicated in the lawsuit and its defense.
Because the technical vendor supply chain continues to grow, companies need to do more than vet their vendors prior to procurement. They need to implement procedures to audit vendor practices to hold them accountable throughout the engagement. Conversely, no SaaS product will ever be perfect and bad actors are lurking behind every corner. Vendors and companies need to use contracts and audits as tools to manage their expectations around risks accordingly.
David Seidman is the principal and founder of Seidman Law Group, LLC. He serves as outside general counsel for companies, which requires him to consider a diverse range of corporate, dispute resolution and avoidance, contract drafting and negotiation, and other issues.
He can be reached at david@seidmanlawgroup.com or 312-399-7390.
This blog post is not legal advice. Please consult an experienced attorney to assist with your legal issues.
Photo Credit: Crowdstrike Outage Renews Debate Over Risks Posed by Microsoft’s Software Dominance – Cloud Wars